Every Team Has a Use Case
SOC analysts, incident responders, MSSPs, compliance teams, and CISOs — all on the same platform.
From alert to answer before shift change.
An alert fires. Your analyst uploads the endpoint collection. SURGE deploys AI agents that parse artifacts, reconstruct timelines, and deliver a forensic answer — before shift change. No escalation backlogs. No waiting on senior analysts.
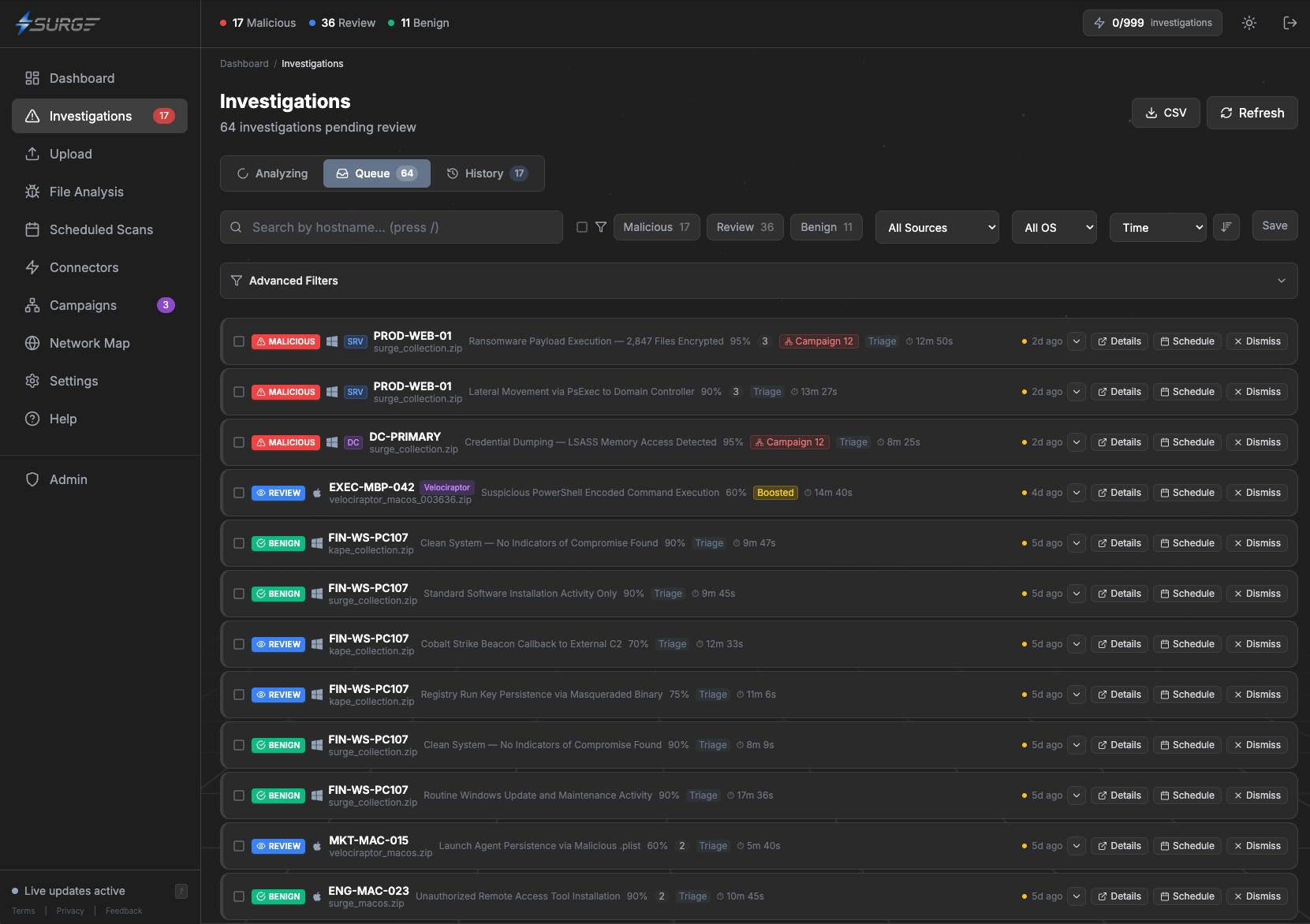
Priority-ranked triage queue — work Critical and High cases first
MITRE ATT&CK technique mapping with risk scoring
AI chat to interrogate findings in natural language
Full investigation before shift change
Your IR team focuses on containment. SURGE handles the forensics.
When an incident hits, every minute counts. Upload collections from affected endpoints and get automated timeline reconstruction, attack chain analysis, and campaign correlation. Containment decisions backed by evidence.
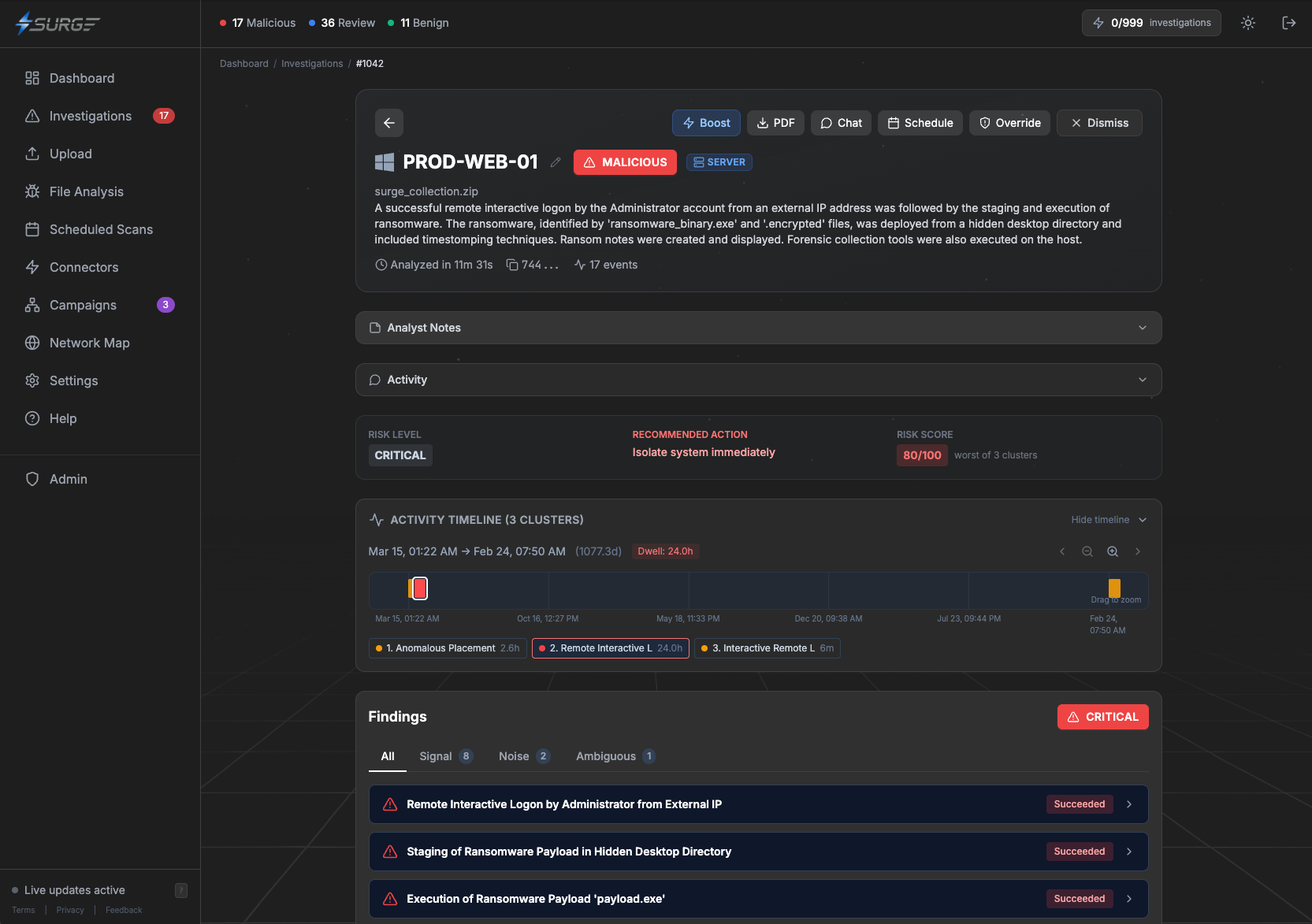
Automated timeline reconstruction across every artifact type
Campaign discovery — correlate IOCs across multiple endpoints
Forensic reports ready for stakeholders and incident response
Clear answers with risk scoring and severity ratings
Serve more clients without hiring more analysts.
Multi-tenant architecture with isolated, encrypted storage per client. Run forensic sweeps across your client base and deliver professional reports — without scaling headcount.
Strict multi-tenant isolation — client data never crosses boundaries
White-label forensic reports with your branding
REST API and webhooks for SOAR/SIEM integration
Team plans with role-based access for analysts and managers
Verify your endpoints are clean. Continuously.
Schedule recurring forensic scans on critical systems. Tag endpoints by compliance framework, detect drift over time, and generate audit-ready evidence.
Scheduled scans with cron support — automate your forensic cadence
Tag endpoints by compliance scope — PCI-DSS, HIPAA, SOC 2, NIST
Drift detection — flag changes between scan intervals
Audit-ready evidence and investigation history
Know exactly which AI agents are running on your endpoints.
SURGE detects AI agent activity at the host level — Claude, Copilot, Cursor, Windsurf, Aider. Distinguish approved tools from shadow AI and govern adoption before it becomes a risk.
GitHub Copilot
v1.234.0
Claude Code
v1.0.16
Cursor
v0.45.6
ChatGPT CLI / Codex
v0.1.2
Windsurf
v1.2.1
Aider
v0.64.1
Session Distribution
97.7%
Approved
2.3%
Shadow AI
4
Endpoints
Detects Claude, Copilot, Cursor, Windsurf, Aider, and more
Distinguish approved agents from shadow AI across your fleet
Alerting on unapproved agent activity with configurable severity
Session artifact recovery — see what agents actually did
See your risk posture. Not a wall of alerts.
SURGE gives security leaders what they actually need — answers, not noise. Fleet-wide risk posture, MITRE ATT&CK coverage gaps, and investigation trends. Know which endpoints are clean and where your blind spots are — at a glance.
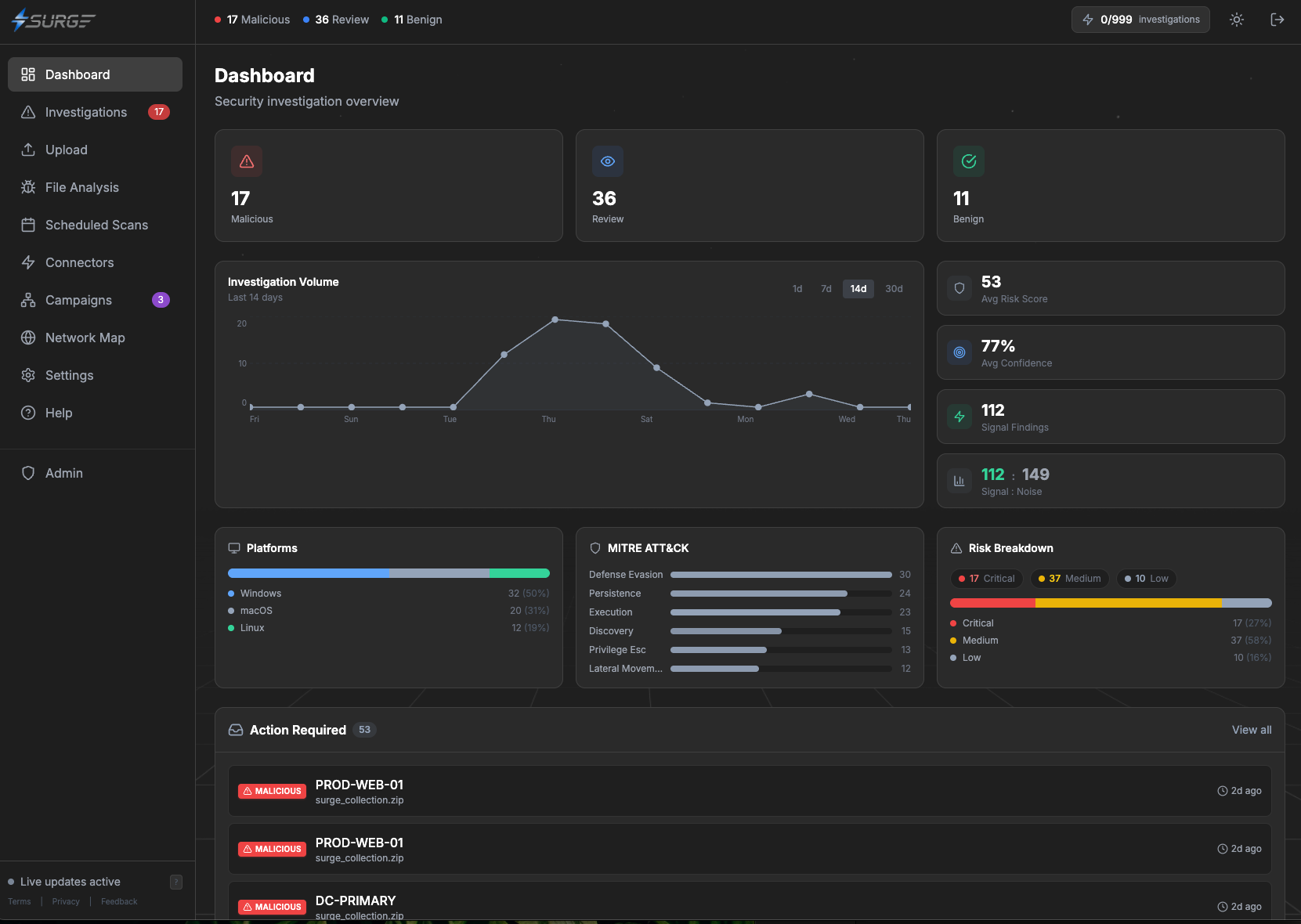
Fleet-wide risk breakdown with trend analysis
MITRE ATT&CK coverage heatmap — see where you're exposed
Investigation volume and trends over time
Compliance posture across frameworks and endpoint groups
Learn more
Contact Us