Everything Under the Hood
The analysis engine, parsers, compliance tagging, and integrations that power every investigation.
Investigation Pipeline
Average Analysis Time
Based on event volume. Servers and high-activity hosts may take longer.
MITRE ATT&CK Coverage
12 tactics · 59 techniques (34 rule-based, 25 contextual)
Init Access
TA0001
Execution
TA0002
Persistence
TA0003
Priv Esc
TA0004
Def Evasion
TA0005
Cred Access
TA0006
Discovery
TA0007
Lat Move
TA0008
Collection
TA0009
C2
TA0011
Exfil
TA0010
Impact
TA0040
Investigation Tools
AI Investigation Chat
Ask questions about any investigation in natural language with full context.
Campaign Discovery
Automatic cross-investigation correlation. Shared IOCs cluster into campaigns with unified timelines.
Triage Queue
Priority-ranked investigations. Work Critical and High first, with bulk actions.
Automated Reports
Forensic reports with evidence, findings, and MITRE mappings. Stakeholder-ready.
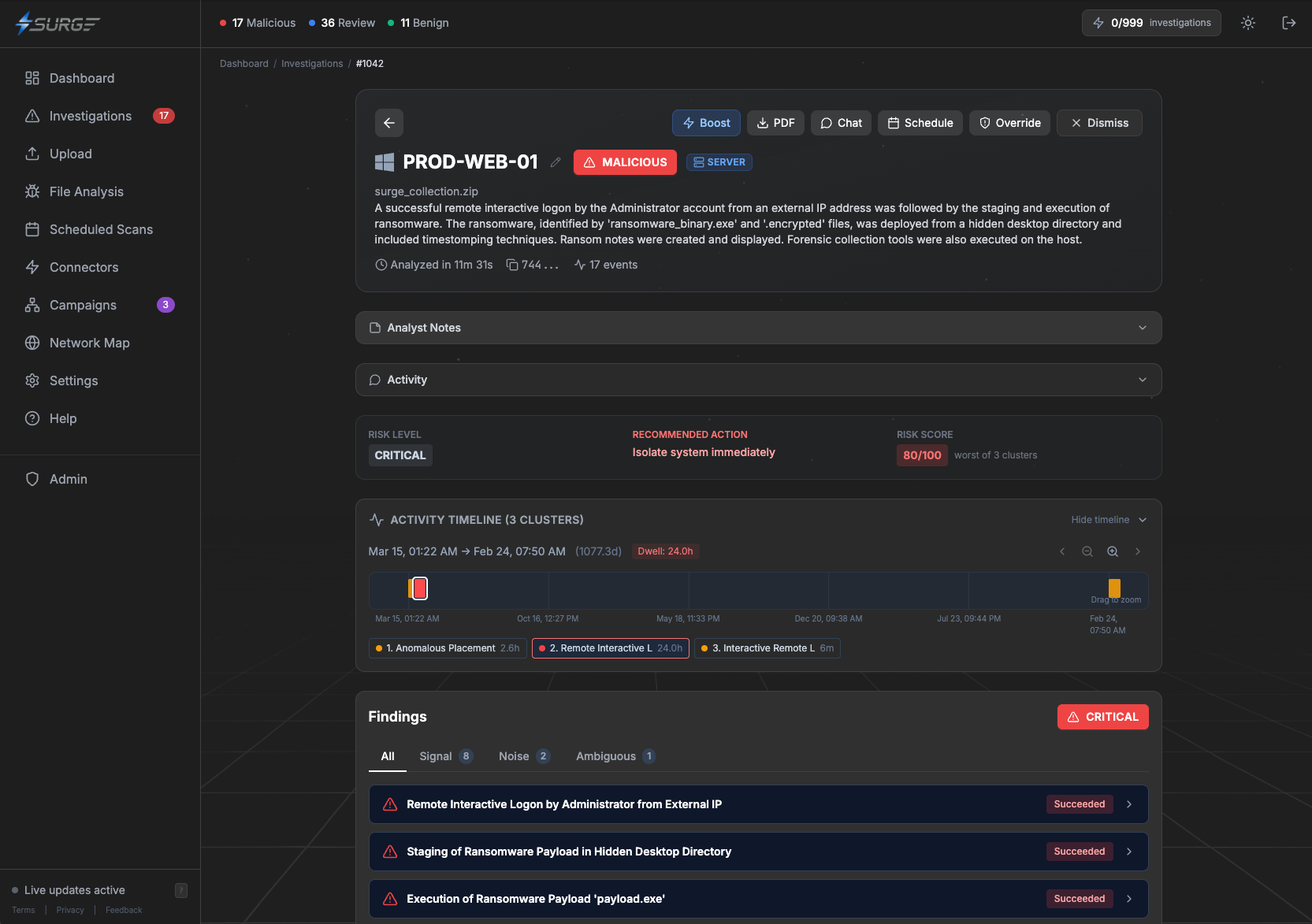
Risk Scoring
Clear answers — Malicious, Review, or Benign — with risk scores and severity ratings.
Boost Analysis
MFT re-parsing and full secondary analysis pass for maximum coverage.
Executive Summary
An active compromise was identified on DESKTOP-CORP-PC1. Encoded PowerShell payloads were executed, credentials were dumped via Mimikatz, and data was staged for exfiltration over HTTPS. Immediate containment and credential rotation recommended.
Findings
MITRE ATT&CK Coverage
Timeline
Compliance & Governance
Compliance Tagging
Tag endpoints by compliance framework — PCI-DSS, HIPAA, SOC 2, NIST. Filter by scope.
AI Agent Detection
Detect Claude, Copilot, Cursor, Windsurf, Aider on endpoints. Flag unapproved shadow AI.
Tenant Isolation
Encrypted, isolated storage per tenant. Your forensic data never crosses boundaries.
Integrations
REST API
Submit collections, retrieve results, manage endpoints. Scoped API keys.
Webhooks
Real-time notifications to your SIEM, SOAR, or ticketing system.
