KNOW WHAT'S TRUE
Autonomous forensic analysis. From collection to answer in minutes.
Artifact Parsers
36
Operating Systems
3
Time to Answer
Minutes
How It Works
Collect. Analyze. Answer.
Three steps. No training, no escalation, no bottleneck.
01
Collect
Run our collector on any endpoint — or bring your own (KAPE, Velociraptor).
Registry Event Logs Prefetch MFT Browser Shell History
02
Analyze
Artifacts parsed, correlated, and assembled into a forensic timeline — automatically.
Timeline Correlate AI Agents MITRE Map Score Cluster
03
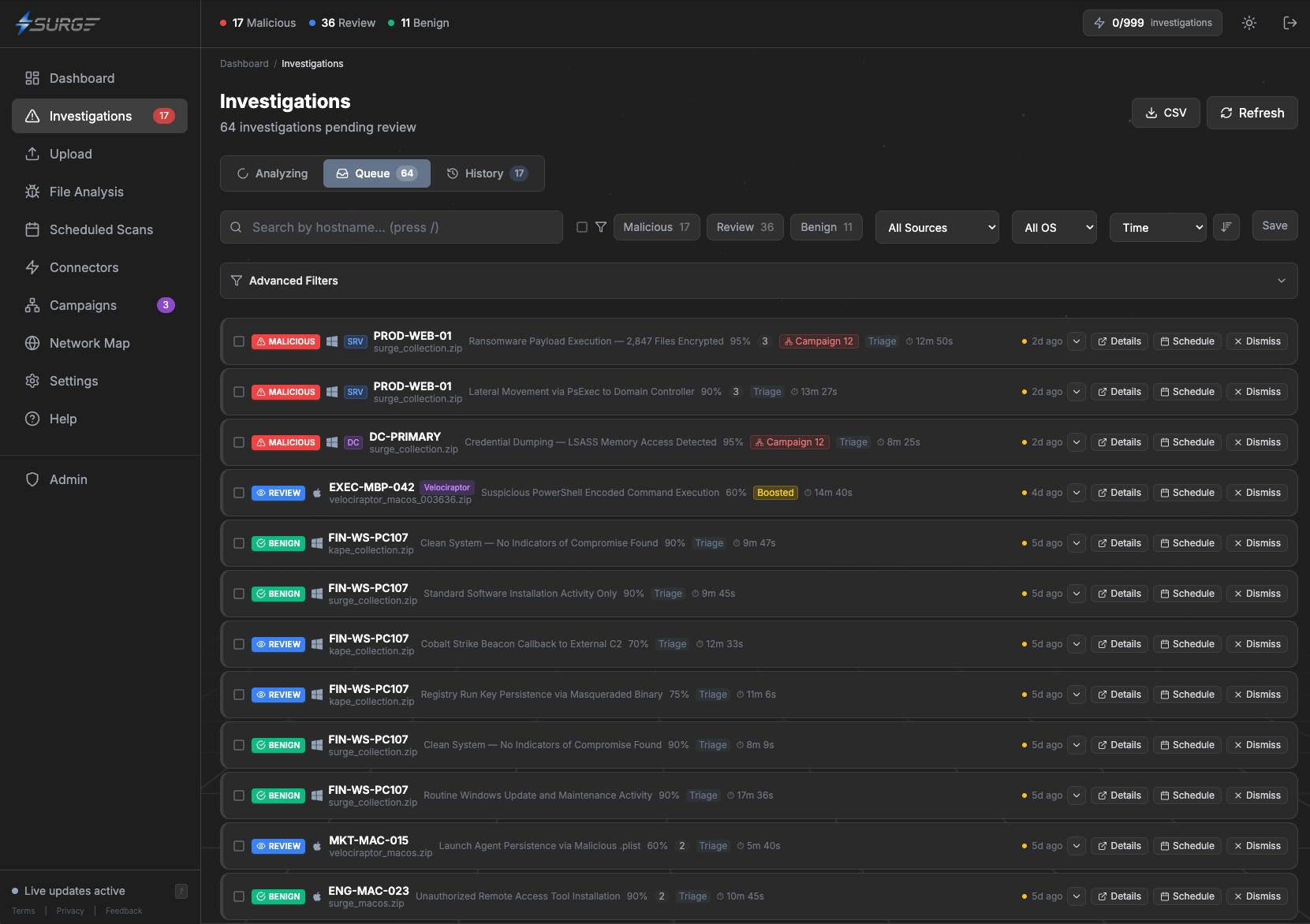
Get Your Answer
Findings, MITRE ATT&CK mappings, risk scoring, and a clear answer.
Findings ATT&CK Risk Score Evidence Report Answer
New Capability
AI Agent Forensics
Detect AI agents on your endpoints. Identify approved tools. Flag shadow AI.
Learn MoreAgent Detection
Claude, Copilot, Cursor, Windsurf, Aider, and more.
Shadow AI Alerts
Flag agents your team hasn't approved.
Session Recovery
Recover transcripts and audit what agents did.
Approval Policy
Define which agents are sanctioned per tenant.
Works With Your Stack
SIEM
SOAR
EDR
CrowdStrike
KAPE
Velociraptor
Windows
macOS Beta
Linux Beta
Enterprise Forensics
Get Your Answer
In Minutes
MITRE mappings. Timeline reconstruction. Structured evidence.
